People usually ask whether an online converter is safe as if the answer were always yes or always no. In practice, the real question is narrower: is this specific tool safe enough for this specific job, with this specific kind of input? A public marketing screenshot, a draft README, and a customer export from production do not carry the same risk. Treating them as the same category leads to bad decisions in both directions. You either avoid fast tools that would have been fine, or you paste sensitive material into a workflow that never should have touched a browser utility in the first place.
That distinction matters because modern work is full of small handoff tasks. Someone needs to compress a few screenshots, validate a CSV before import, preview Markdown before it lands in docs, or convert config data between JSON and YAML. None of those jobs is complex, but each one can interrupt the larger project if the tool introduces setup overhead, weak privacy expectations, or a confusing processing model. That is the gap browser utilities are supposed to close. The point is not to replace every CLI, editor, or build step. The point is to remove friction from the small jobs around them.
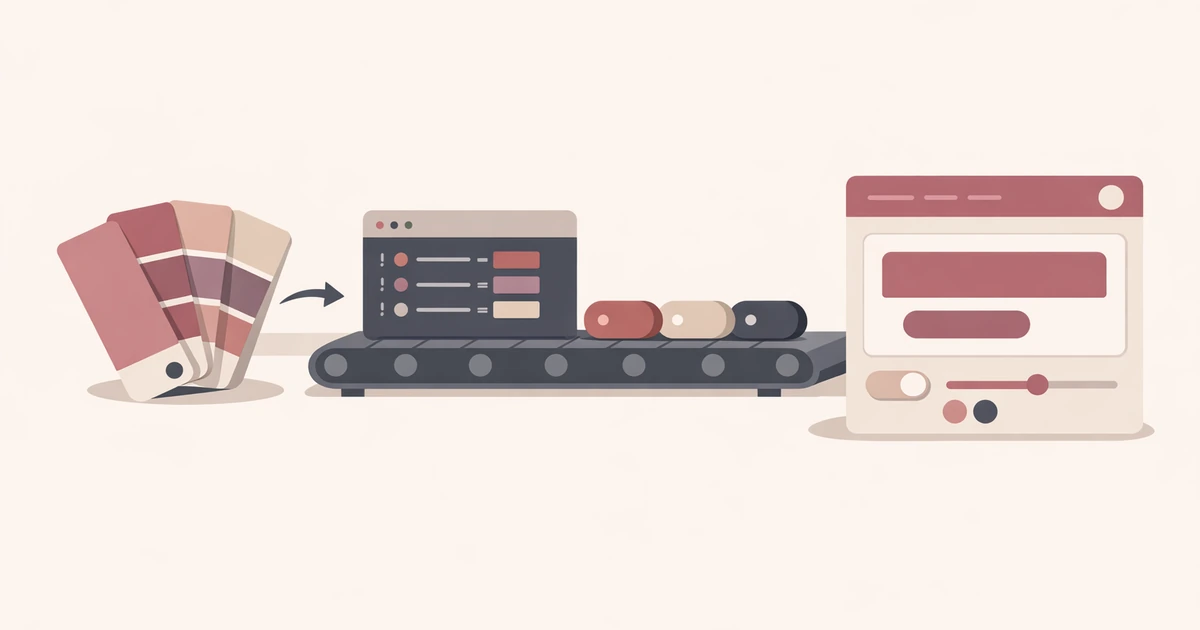
If you have read Introducing Converty, you have already seen that the product is built around that exact pattern. The useful follow-up question is what you should check before trusting any similar tool with work material.
The first thing to check is where the work actually happens
The biggest practical difference between online converters is whether the input stays inside the browser tab or leaves the browser for server-side processing. That one detail tells you far more than a vague promise about productivity.
For text and structured data, a good browser-based tool can often keep everything local. In Converty, that is the model for the color converter, the case-and-slug tool, the CSV validator, the Markdown validator, and the JSON / YAML / TOML converter. The work happens in the tab, which means the decision is less about file retention on a server and more about whether you are comfortable placing that material in a browser context at all. For many day-to-day tasks, that is exactly what you want: paste a snippet, inspect the output, copy what you need, and move on.
That does not mean "browser-based" automatically equals "safe." It means you now know the class of risk you are judging. A browser-only tool reduces server exposure, but it does not magically make sensitive information harmless. If the content is a production secret, an unreleased customer data extract, or a contract you would not paste into a public web form under any circumstances, the safer answer is still not to use a general browser utility. The right comparison is not browser tool versus no risk. It is browser tool versus the sensitivity of the material.
When uploads are required, narrow processing matters more than marketing copy
Some tasks cannot stay local because they depend on binary file handling, export generation, or image encoding. That is where the second question comes in: if an upload is required, how narrow is the server-side step?
In Converty, the WebP Converter and the Favicon / App Icon Generator are file workflows, so they use server-side processing. The useful detail is not simply that an upload occurs. The useful detail is that the upload exists only long enough to finish the requested job and return the result. That is the kind of operational boundary you want to see in any tool handling work assets. A converter does not need to become your asset management platform, your archive, or your collaboration hub. It should handle the transformation and get out of the way.
That principle is more important than polished reassurance language. A narrow workflow is easier to trust because it has fewer moving parts. If a tool needs an account, asks you to organize assets in a dashboard, or implicitly turns a quick transformation into a content-management system, the trust decision becomes larger. You are no longer evaluating a converter. You are evaluating a platform.
Match the workflow to the sensitivity of the file
The safest way to use online converters at work is to sort inputs into three broad buckets before you do anything else.
The first bucket is low-risk operational material: screenshots for documentation, placeholder graphics, public-facing content snippets, Markdown drafts, non-sensitive config examples, or CSV samples with fake or scrubbed rows. These are the jobs browser tools are best at because speed matters more than heavy process.
The second bucket is internal but still manageable material: staging data, in-progress launch assets, configuration files without secrets, or documentation drafts that are not yet public but are not deeply regulated either. Here you want to be more deliberate. A browser-only workflow may still be fine. A narrow upload-based workflow may also be fine. The difference is that you should check it on purpose instead of defaulting to convenience.
The third bucket is material that should not be casually pasted into generic browser utilities at all: customer exports, regulated records, secrets, credentials, private keys, production logs with user data, or contract-heavy files that trigger legal or compliance obligations. At that point the right tool is usually one your company already controls, or a local workflow with clear policy coverage. Speed is no longer the main variable.
This is the point many teams skip. They evaluate tools in the abstract instead of classifying the job first. Once you classify the job, the tool choice gets easier.
A realistic launch-day workflow makes the tradeoff clearer
Imagine a small team preparing a launch page. Marketing has draft screenshots. A developer has a short block of Markdown for release notes. Content needs a clean slug and a favicon package before the deploy goes out. Nothing in that set is highly sensitive, but nobody wants the work to sprawl across five apps and a pile of one-off scripts.
This is where a narrow browser utility stack makes sense. The team can run the screenshots through the WebP Converter, generate browser icons with the Favicon / App Icon Generator, check the release-note formatting in the Markdown Validator, and normalize the launch title in the Case / Slug / Escape tool. The questions that matter are concrete: which tasks stay in the browser, which ones require short-lived processing, and whether the material itself is appropriate for a lightweight web workflow.
Notice what does not happen in that example. Nobody pretends the browser utility is now the source of truth for the launch files. Nobody assumes it should handle secret config or customer data. The tool is being used as a transformation layer around the real work, which is exactly where it is strongest.
If your team publishes often, the same logic also applies to editorial QA. A Markdown draft that is headed for docs or a CMS is a good fit for a browser check. That is one reason the next article in this wave, How to Catch Markdown Issues Before Publishing, matters. It turns a vague "looks fine to me" check into a more defensible pre-publish pass.
A practical checklist before using any online converter
You do not need a long security questionnaire for every small utility task, but you do need a repeatable filter.
- Ask whether the work stays in the browser or leaves the browser.
- If upload is required, ask how narrow the processing step is and whether the tool stores anything beyond the transformation itself.
- Decide whether the input belongs in a browser utility at all, based on sensitivity rather than convenience.
- Prefer tools that do one short job well over tools that expand the task into an account-based workflow you do not need.
- Keep public, low-risk, and lightly internal materials separate from anything regulated, secret, or customer-specific.
That checklist is simple on purpose. The goal is not to turn every utility decision into policy theater. The goal is to stop treating every file the same way.
The safest tool is the one that fits the job without expanding it
Most teams do not need one universal answer to the question "are online converters safe?" They need a faster way to decide whether this tool fits this task. When the work is browser-based, low-risk, and operationally narrow, a utility like Converty can save time without creating unnecessary process. When the work is more sensitive, the same discipline that makes a browser tool useful should also tell you to step away from it.
Start with the FAQs if you want the concrete handling details across Converty's tools. Use Introducing Converty for the broader product context. And if your immediate concern is content QA rather than file upload risk, continue with How to Catch Markdown Issues Before Publishing.